Local News
Thief Tricks Students to Steal Band Instruments: Plano Police
PLANO, TX – A man tricked students at Plano East Senior High School so he could steal band instruments, police say.
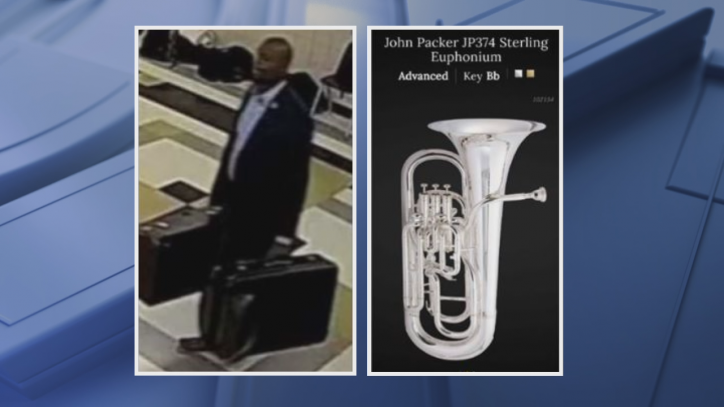
Police released a surveillance image of the suspect leaving the school with two instruments in his hands. He was dressed in a blazer and a button-up shirt.
“He even had a Gucci belt on,” said PESH senior Joshua Ellis, who plays the euphonium — a smaller version of the tuba — one of the instruments stolen.
Ellis says band members store their instruments in the band hall on campus. He says he realized his euphonium was missing when he went to play it this week.
Plano police say the man went to the school last Thursday about 6 p.m., convinced students he was there to pick up instruments for repair, then walked out with a baritone saxophone and Ellis’s euphonium which he bought for around $4,000.
“How fast he did it, how smoothly he did it, he knew what he was doing,” Ellis said.
Ellis says the man hit when band teachers and students were headed out of town for a music convention.
“It has to be somebody who knows,” Ellis said.
Plano police say the suspect was seen leaving in a red four-door vehicle.
Crimestoppers is offering up to a $5,000 reward.
In a statement, Plano ISD said:
“Plano East Senior High School and Plano ISD are cooperating with the Plano Police Department as they investigate a theft that occurred after school hours on February 13. The suspect allegedly stole two instruments from the band hall after entering the building and convincing students he was there to pick up instruments for repair.
“The brazenness of a such an act—stealing from our students—is appalling,” said Executive Director for Safety and Security Services Joe Parks. “We encourage anyone with information about the incident or the suspect to contact the Plano Police Department at 972-424-5678 or Campus Crime Stoppers at 877-373-8477.”
The school and district are carefully reviewing this incident to determine if any adjustments need to be made to security protocols, and whether additional reinforcement of existing practices may be needed.”